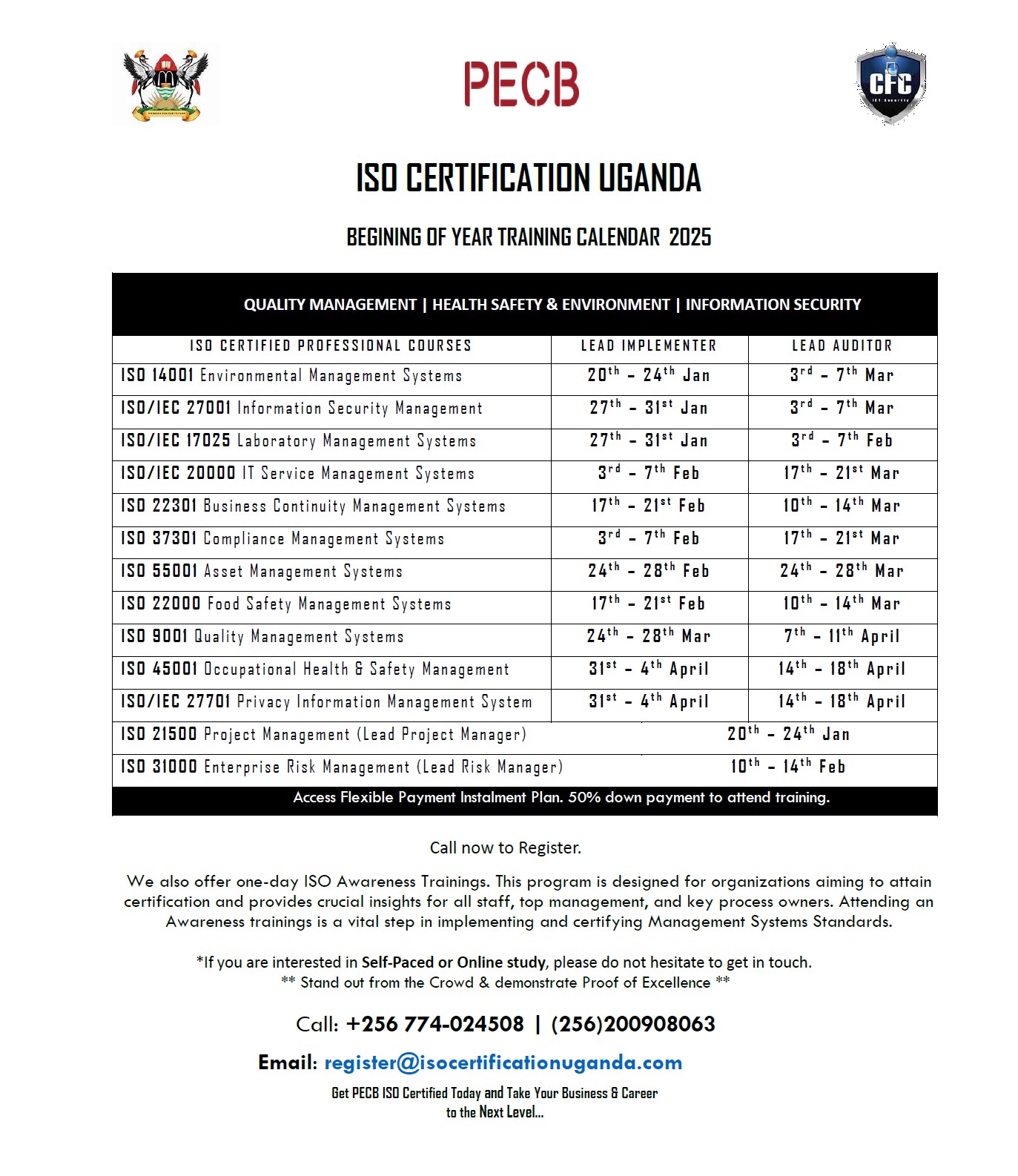
ISO CERTIFICATION. AUDIT & TRAINING
Over fifty (50+) Standards
Management Systems Implementation Support for Organizations
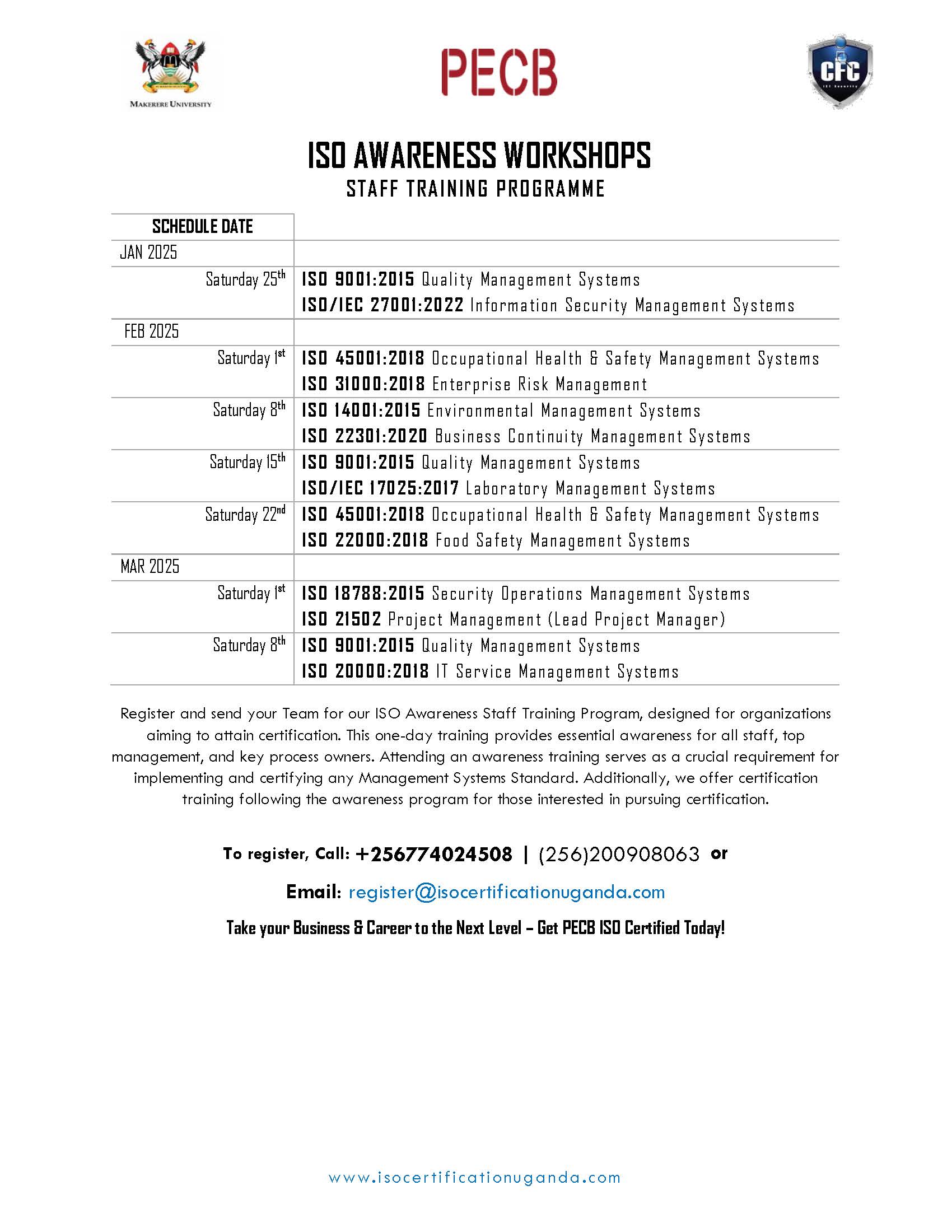
Awareness Training for Top Management & Staff + ISO Documentation Consultancy
ISO Certification for Individuals & Organizations
Based on best practices in Industry
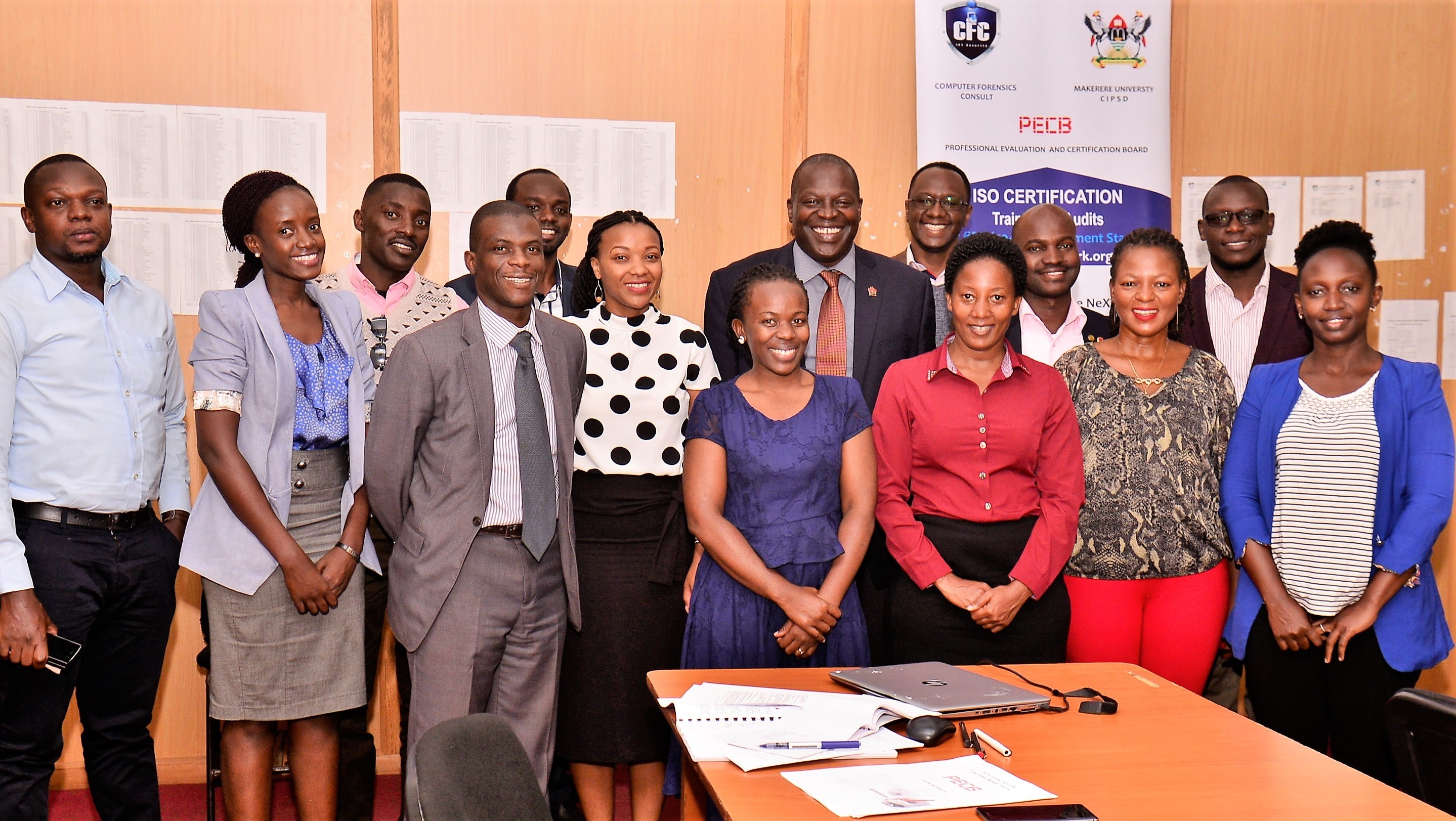
ISO Certified Trainings hosted @ Makerere University
Learn more about our exciting Horizon Program and how it can benefit your organization.
College of Computing & Information Sciences (CoCIS)
Center for Innovation & Professional Skills Development (C I P S D)